At a high level, the difference between a SOC 2 Type I and Type II comes down to design vs. performance. A Type I report is a point-in-time snapshot, showing that your controls are thoughtfully designed as of a specific date. A Type II goes a step further, demonstrating that those controls operate effectively over time (typically 3 to 12 months). In practice, a Type I shows you’ve set things up correctly, while a Type II proves you can run them consistently.
Because of this difference, the decision often gets reduced to efficiency and sequencing. Teams weigh whether it makes sense to move quickly with a Type I first, or whether it is more efficient to focus on the Type II path from the start and avoid duplicating effort across both.
Moreover, the same question tends to get asked:
Do we need Type I before Type II, or can we go straight to Type II?
It is a reasonable question, but it is often asked too early, before there is a clear understanding of what each assessment type requires for the participant to find success.
The key factors are not just about time and money; they also require consideration of the following three variables:
- Whether your control environment is ready to withstand external scrutiny over time;
- How quickly a report is needed; and
- What your customers will accept.
Therefore, the first and most critical question one should ask before committing to a SOC 2 assessment is: Does our current state support the assessment type that we are choosing?
Type I and Type II Measure Different Things
Before comparing the different SOC 2 paths, it is important to comprehensively clarify what Type I and Type II measure, since the decision between them depends on how these differences apply in practice.
Type I:
The intent of a Type I audit is to confirm that controls are properly designed and were implemented and operating as intended at a specific point in time.
An auditor reviews your policies, documented procedures, and the controls you have in place. They will then issue a report, documenting their opinion as to the controls in place, if they were designed appropriately and if they effectively met the relevant Trust Services Criteria (Security, Privacy, Confidentiality, Availability and Processing Integrity).
Type II:
The auditor reviews the same controls as required for the Type I but also creates sample sets and collects evidence that those controls function consistently throughout the audit window. This includes access reviews, incident records, change management documentation; evidence that your security program is operational, not theoretical.
Both reports are issued by an independent CPA firm and evaluated against the AICPA’s Trust Services Criteria. The distinction is not simply point-in-time versus over-time. It is design assurance versus operational assurance.
Five Paths to SOC 2 Compliance
With the Type I and Type II distinction in mind, the way organizations approach their first SOC 2 engagement depends heavily upon how ready the controls are to be assessed. At Drummond, we typically see five paths to SOC 2 compliance, depending on maturity and needs.
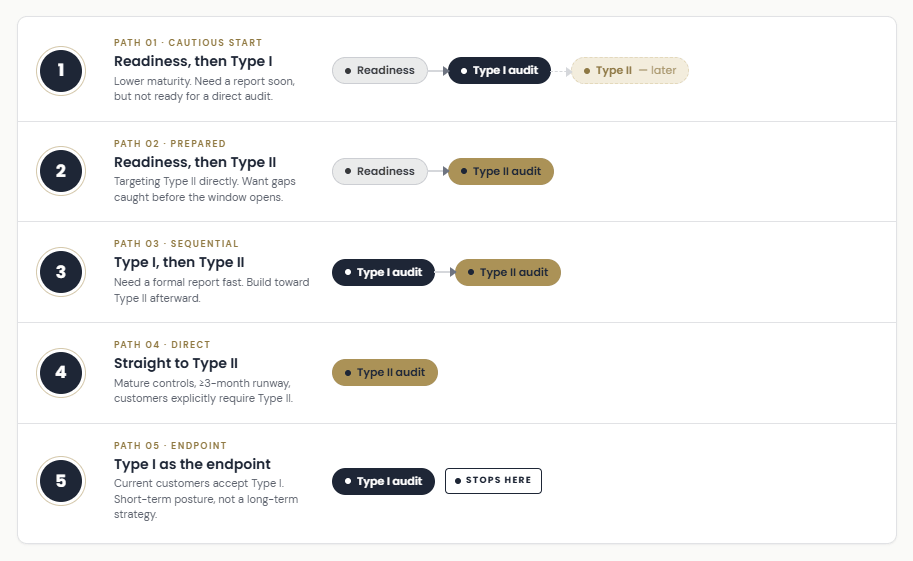
Path 1: Readiness Assessment, then Type I
Organizations on this path need a formal, auditor-issued report, typically to respond to a customer or prospect request, but are not confident enough in their control maturity to commit directly to a Type I audit. The readiness assessment de-risks that commitment. It surfaces what needs to be corrected before an auditor evaluates the design of controls under formal conditions.
A readiness assessment is not a pre-audit checkbox. It is a structured diagnostic. An experienced auditor evaluates your controls, documentation, and evidence, where available, against the same criteria used in a formal audit. This is done prior to an audit to determine:
- Gaps in policy coverage;
- Inconsistent control operation; and
- Evidence that would not suffice during an audit.
This allows organizations the time and peace of mind to correct issues prior to the Type I audit. Because this path allows more time and ease, it is generally the path taken by those who have fewer controls in place, documentation, etc., or those that have larger organizations, requiring significant time for remediations.
Path 2: Readiness Assessment, then Type II
This path fits organizations targeting Type II directly but wanting an honest picture of their control environment before the formal observation period starts.
A readiness assessment, or gap assessment, allows these issues to be addressed before an observation period begins. Findings caught in a readiness phase disappear quietly, while findings from a formal Type II audit appear in the report.
That distinction matters more than most first-time organizations realize. A SOC 2 report is shared with customers, prospects, and procurement teams. Exceptions in that report are visible to everyone who reads it.
For organizations that have never been through an external audit, who would not benefit from a Type I report for their clients, a readiness assessment is the most defensible starting point for a SOC 2 Type II audit. For a deeper look at what preparation involves, Drummond’s SOC 2 Type 2 Readiness Playbook covers the six steps in detail.
Path 3: Type I, then Type II
This path suits organizations that need a formal report quickly and have enough confidence in their control design to proceed to Type I directly.
A Type I audit can be completed in four to eight weeks from kickoff to report. For an organization facing a prospect deadline or an enterprise customer request, that timeline is often the deciding factor. The Type I report satisfies the immediate need while the organization builds toward Type II.
There is also a structural argument for this sequence beyond speed. Type I forces the documentation exercise that Type II will require anyway, formalizing policies, mapping controls, establishing evidence practices. Completing that work before the Type II observation period reduces internal burden during the window when consistent operation needs to be demonstrated.
Even when teams feel ready to go straight to Type II, Type I is often still used as the starting point because it establishes that baseline documentation and control clarity before the observation period begins. In practice, Type II depends less on confidence in design and more on having time-stamped evidence of controls operating consistently, which Type I helps put in place before that measurement window starts.
Path 4: Straight to Type II
This is the right path for organizations with a documented, mature control environment, a minimum three-month window before the report is needed, and customers explicitly requiring Type II.
The case for going straight to Type II is straightforward:
- It avoids the cost of two separate audits.
- It delivers the report that enterprise procurement teams require.
- If controls are genuinely ready, the observation period is a confirmation process rather than a test.
The risk is equally straightforward. Organizations that overestimate their control maturity and commit to Type II without a readiness review are the most likely to surface findings mid-observation period. Moreover , control rework during an active audit window can significantly extend timelines, weaken evidence narratives, and produce a report that reflects a compliance program still finding its footing.
Path 5: Type I as the Endpoint
Some organizations need only to demonstrate security commitment. Their current customers accept Type I, and their timeline or budget does not support a Type II observation period. Type I as an endpoint is a legitimate choice in that context.
The honest framing: it works until the customer mix changes, making this path exceedingly rare.
As organizations move upmarket into enterprise accounts, procurement teams that previously accepted Type I begin requiring Type II. That shift typically arrives faster than expected. Treating Type I as a permanent compliance posture may be a reasonable short-term decision. It is not a long-term strategy.
Before You Commit to a Path
Each of the five paths is right for a specific situation. The problem is that most organizations make the decision based on what they want their timeline to be rather than what their control environment supports.
The failures that occur because of this are rarely dramatic. Instead, they surface as inefficiency, rework, and credibility gaps after the commitment has already been made.
To avoid this, organizations can use the following three variables to determine the right SOC 2 path before the audit clock starts.
1. Control Maturity
Are your controls formally documented, consistently operated, and evidenced? Or were they recently implemented, partially documented, or not yet reviewed by anyone outside your team?
Low maturity points toward a readiness assessment first. High maturity supports going straight to Type II. Most organizations land somewhere between those poles, which is where an external readiness assessment produces the most value. It converts a subjective internal confidence level into an objective gap analysis.
2. Timeline
How much time is available before a report is needed? A Type I audit can be completed in four to eight weeks. A Type II audit requires a minimum three-month observation period, with fieldwork completing at the end of that window or after, putting total first-audit timelines at four months or longer. A hard deadline inside sixty days points toward Type I or readiness-first. A deadline allowing four or more months opens every path.
3. Stakeholder Requirements
What has the customer or prospect asked for? “We need SOC 2” and “we need a Type II report before contract execution” are different requirements. Enterprise procurement teams increasingly expect Type II, but not universally and not always with the same urgency. Know the specific requirement before selecting a path. A conversation with your prospect’s security team often clarifies what the written vendor requirement left ambiguous.
Get the Path Right Before the Clock Starts
Most SOC 2 decisions go wrong before the audit starts. Not because organizations chose the wrong auditor or underestimated the workload, but because they committed to a path before honestly assessing what their control environment could support.
The five paths exist because control maturity, timeline, and stakeholder requirements vary across every organization that walks into a first audit. There is no universally correct sequence. There is only the sequence that matches your current state to the report your customers actually require.
In practice, that means the real risk is not execution, it is misalignment early in the process that compounds later when evidence collection and testing are already underway. Small gaps in readiness do not stay small once they enter an audit cycle.
Drummond’s audit team has guided organizations through each of these paths: first-time audits, readiness gaps caught before they became audit findings, and Type II engagements that ran cleanly because the foundation was established early. That perspective is most valuable before the observation window begins, when the path is still a decision, not a constraint.
Because once the window opens, you are no longer preparing for the audit, you are being measured by it.
