Two companies. Same industry. Same regulatory requirements.
Both conduct penetration testing. One does it when an auditor requires it.
The other does it every year, as part of their internal security processes. And sometimes multiple times a year to address changes in their systems and environment.
The difference between them is measurable.
The first company treats testing as a compliance event. The second treats annual testing as a business discipline. Over time, that discipline compounds and becomes part of how the organization operates, not just how it audits.
That is the difference.
Annual penetration testing is not just about identifying vulnerabilities. It is about creating a structured, recurring mechanism that strengthens risk posture, provides financial leverage, and helps increase revenue year after year. When done consistently, it becomes a signal to the market, to insurers, and to internal stakeholders that security is proactively managed.
Once in a While No Longer Works
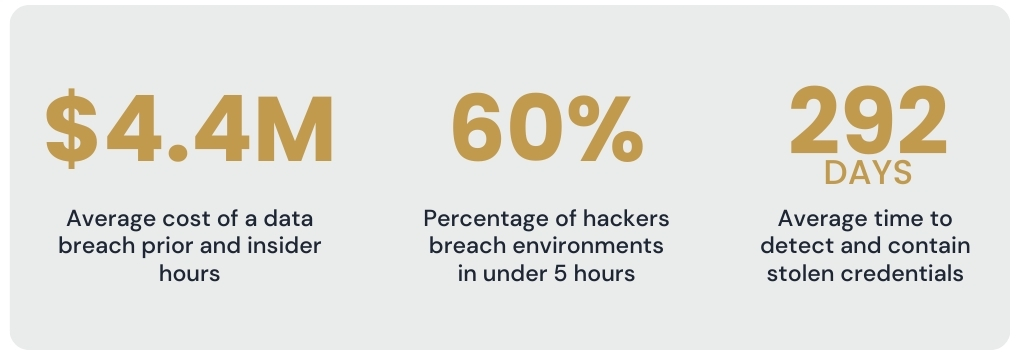
The threat landscape moves fast, much faster than most organizations realize. In 2024, IBM reported the average cost of a data breach reached $4.4 million, up 10 percent from the previous year. At the same time, attackers are moving with unprecedented speed. Nearly 60 percent of ethical hackers say they can breach an environment within five hours of finding a weakness.
In real-world environments, compromise can happen far faster than most organizations expect. It is entirely possible for an attacker to obtain full Active Directory administrative permissions within minutes if something as simple as plaintext credentials exists in a hidden public file share. Many organizations are unaware that such exposures are present in their own environments.
This is the practical reality of modern risk. Seemingly minor oversights, legacy configurations, or forgotten assets can provide direct paths to domain-level compromise. Attackers do not rely on a single catastrophic flaw. They chain small weaknesses together quickly and methodically.
The stakes are compounded by prolonged recovery times. Stolen credentials, now the most common initial attack vector, take an average of 292 days to detect and contain. In other words, even a brief window of vulnerability can translate into months of risk exposure and millions in potential losses.
Testing only occasionally assumes that your environment, technology, and threat exposure remain static between assessments. They do not.
Cloud migrations, new integrations, API expansions, product launches, vendor relationships, and infrastructure changes continuously reshape exposure. Even minor configuration shifts can introduce unintended weaknesses. Annual testing creates a structured checkpoint that recalibrates your understanding of risk every year. It forces the question: what has changed, and what does that change mean for our security posture?
Testing once is a snapshot. Testing annually creates visibility over time.
Establishing this annual rhythm does more than maintain visibility over evolving risks. When executed thoughtfully, a single, well-scoped penetration test can also satisfy multiple regulatory obligations at once, creating efficiency and reducing redundancy.
Compliance Is the Baseline. Maturity Is the Advantage
Yes, PCI DSS 4.0 mandates annual external and internal penetration testing. HIPAA, SOC 2, and ISO 27001 all carry expectations around regular assessment and validation.
But strategic organizations are not testing because they have to.
They are testing annually because it creates leverage beyond compliance.
A single, well-scoped annual test can satisfy multiple regulatory obligations simultaneously. Instead of scrambling for framework-specific assessments, organizations can align one comprehensive engagement to cover PCI DSS, HIPAA, SOC 2, and ISO 27001 requirements at once. That coordination reduces redundant effort, simplifies documentation, and centralizes remediation tracking.
This efficiency lowers compliance friction and audit fatigue. It also allows security and IT teams to focus their energy on actual risk reduction instead of juggling overlapping assessments or duplicating work for each framework. By consolidating testing efforts, organizations gain a clearer view of their overall security posture and maintain consistent standards across all systems and controls.
But the real return shows up outside the audit.
Where Strategic Organizations Pull Ahead
The organizations that gain the most from annual testing are not doing anything extraordinary. They are doing something consistent and intentional. By treating each engagement as a strategic input into real business decisions, they experience the following benefits.
Sales Momentum and Customer Trust
Procurement teams increasingly require documented evidence of recent penetration testing. Not self-attestations. Not marketing claims. Evidence.
When testing is conducted annually, sales teams are never scrambling to commission an assessment in the middle of a deal cycle. They can provide current documentation immediately, answer scope questions confidently, and demonstrate a documented remediation history across multiple years.
That history matters.
One test shows effort. Three consecutive annual tests show maturity.
Over time, customers begin to recognize patterns of discipline. Security questionnaires become easier because the answers are already supported by evidence. Objections are addressed earlier in the conversation. Trust is established before doubt has a chance to grow.
Annual cadence builds that pattern. It shifts security from a reactive conversation to a proactive differentiator.
Risk Decisions That Improve Year Over Year
Automated scans generate large volumes of findings. Without context, prioritization becomes reactive and sometimes arbitrary.
Automated tools absolutely have value. They are effective at identifying common misconfigurations and surfacing known issues quickly. Most experienced penetration testers rely on them to improve efficiency.
But automation alone captures only a fraction of what a skilled tester can uncover. In practice, automated scanning typically identifies only a fraction of the vulnerabilities that can be uncovered during a comprehensive manual engagement.
The difference lies in human judgment. A skilled tester evaluates how vulnerabilities interact, which systems matter most to the business, and how an attacker would realistically pivot across the environment. The process remains highly manual. Tools support the work, but they do not replace the expertise required to interpret results, chain weaknesses together, and simulate real-world attack paths.
Penetration testing provides context that automation cannot. It shows what is truly exploitable in your environment, how vulnerabilities can be combined, and what the likely business impact would be if those weaknesses were exploited.
When this exercise happens annually, organizations gain something more powerful than a vulnerability list. They gain trend data and operational insight.
Are critical findings decreasing year over year?
Are certain systems repeatedly exposed?
Are development practices producing fewer high-severity issues over time?
That visibility allows leadership to measure security program effectiveness in concrete terms.
Another overlooked benefit of recurring testing is institutional learning.
Each penetration test creates a feedback loop not only for security teams, but also for developers, system administrators, and managerial staff. Teams gain exposure to real attack techniques. They learn how misconfigurations are exploited, how weak architectural decisions are abused, and how small coding oversights can escalate into major exposure.
Over time, this changes behavior. Developers begin writing more defensively. Infrastructure teams recognize risky configurations earlier. Leadership develops a clearer understanding of how technical weaknesses translate into business risk.
Penetration testing becomes as much about raising organizational security awareness as it is about identifying vulnerabilities. With annual repetition, that awareness compounds.
Insurance and Financial Leverage
Insurers evaluate security posture with increasing scrutiny. Underwriters examine testing frequency, scope, provider independence, and documented remediation when determining policy terms.
Frequency matters.
An organization that tests sporadically signals inconsistency. An organization that tests annually demonstrates operational discipline and governance maturity.
That discipline can translate into lower premiums, improved coverage limits, and more favorable deductibles. More importantly, in the event of a claim, documented annual testing strengthens the argument that reasonable security practices were maintained. It becomes part of the evidence trail that supports payout eligibility.
Over time, annual testing is not just a cost center. It becomes a component of financial risk management and balance sheet protection.
Organizations that rely only on lightweight scans and surface-level checks often believe they are covered because no critical alerts have appeared. In reality, shallow assessments frequently miss exploitable weaknesses.
When comprehensive testing is deferred, companies increase the likelihood that a motivated attacker will find what automated scans do not. In breach scenarios that lead to ransomware or operational disruption, security investment often increases dramatically after the fact. By then, the financial and reputational damage has already occurred.
Consistent annual testing shifts that investment forward in time, where it reduces exposure instead of reacting to it.
Building an Effective Annual Testing Discipline
The strategic advantages of annual penetration testing are clear. It strengthens sales positioning, improves risk decisions, and enhances insurance leverage.
But none of those outcomes happen automatically.
An annual test only creates compounding value if it is treated as an operational discipline. Without structure, integration, and follow-through, testing becomes just another recurring expense.
The organizations that see measurable returns from annual testing do not simply schedule an assessment each year. They build a repeatable system around it. They treat testing as part of an ongoing cycle of evaluation, remediation, measurement, and refinement through the following principles.
Integrate Testing Into Security Operations
Annual penetration testing should feed directly into your broader security program.
Findings must move into vulnerability management workflows with clear ownership and defined remediation timelines. Threat models should be updated based on real attack paths discovered during testing. Detection and response capabilities should be evaluated against the techniques testers successfully used.
Penetration test reports should function as roadmaps for security refinement, not static documents stored for audit purposes. The business impact analysis provided by testers enables prioritization based on real-world risk, allowing teams to focus on what materially reduces exposure.
When testing is integrated in this way, each annual cycle strengthens the security program rather than temporarily disrupting it.
Evolve Scope with the Business
Testing the same systems the same way every year because it feels familiar limits effectiveness.
As the organization evolves, so does its attack surface.
Break the ecosystem into logical components such as applications, networks, cloud infrastructure, and identity systems. Test each component as frequently as budget allows. Dynamic code reviews and architectural assessments can be just as valuable as traditional black box penetration tests, particularly for rapidly evolving application environments.
Different testing formats uncover different classes of risk. Rotating methodologies and maintaining regular cadence increases coverage depth and reduces blind spots. Over time, this structured variety strengthens both technical resilience and organizational maturity.
Establish Continuous Improvement Metrics
Consistency allows for measurement.
Organizations should track year over year metrics such as time to remediation, vulnerability volume by severity, recurring exposure patterns, and control maturity progression. These indicators reveal whether security posture is improving, stagnating, or regressing.
Multi-year testing history becomes operational intelligence. It highlights systemic weaknesses, validates process improvements, and provides concrete evidence of program maturity.
Without annual repetition, trend analysis is impossible. With it, security becomes measurable.
Choose and Retain the Right Testing Partner
The effectiveness of an annual penetration testing program depends heavily on the expertise of the third-party service provider.
When selecting a provider, look for relevant industry experience, familiarity with your technology stack, and a deep understanding of applicable compliance frameworks. Technical depth and proven methodology are far more important than cost alone.
Building a long-term relationship with a trusted testing partner adds significant value. Over multiple annual engagements, the provider gains contextual knowledge of your environment, architecture, and historical vulnerabilities. This continuity allows them to identify subtle risks, provide more targeted recommendations, and conduct testing more efficiently.
Frequent changes in third-party providers can disrupt this accumulation of knowledge, forcing the organization to repeatedly reestablish context and reducing the overall insight gained from each engagement. Choosing the right partner and maintaining that relationship ensures your annual testing program delivers maximum strategic and operational benefit.
Plan Remediation Before Testing Begins
Annual testing creates predictable remediation cycles. That predictability should be planned for.
Development, infrastructure, and security teams should understand their responsibilities before testing starts. Budget and resource allocation for post-test remediation should be anticipated rather than treated as unexpected work.
Organizations that plan remediation capacity in advance close findings faster and reduce exposure windows. Those that do not often see vulnerabilities linger while teams compete for bandwidth.
Make Testing Work for Your Business
Security is not merely a compliance requirement. It is a visible signal of how an organization operates.
At Drummond, our certified testing team designs penetration testing programs that align directly with business objectives, strengthening security posture while supporting PCI DSS, HIPAA, SOC 2, and ISO 27001 requirements. Testing is not treated as an isolated event, but as part of a structured, repeatable discipline that integrates with operations, compliance, and risk management.
The results are tangible. Organizations that test consistently reduce potential breach exposure, accelerate deal cycles with ready documentation, improve their position with insurers, and build durable customer trust. Those that approach testing as a periodic obligation may satisfy auditors, but they often forfeit the compounding advantages that consistency creates.
Annual penetration testing delivers value. The real opportunity lies in approaching it deliberately so that each year strengthens security maturity, reinforces market credibility, and contributes to measurable business outcomes.
